Container-native architectures have transformed how applications are deployed and scaled, but they have also introduced a range of new security challenges, particularly around runtime behavior. While vulnerability scanning, configuration audits, and identity controls provide essential safeguards, they cannot reveal what applications actually do once deployed. In highly dynamic environments such as Oracle Kubernetes Engine (OKE), runtime visibility becomes a critical missing piece of a puzzle.
This article presents a full analysis of how Falco, an open-source behavioral monitoring engine, addresses runtime blind spots in OKE. Unlike static scanning or policy-based enforcement, Falco continuously examines node-level events and workload behavior to identify suspicious or unexpected activity in real time. This report outlines Falco’s operational relevance, architectural role, high-value use cases, and overall strategic importance to our cloud security posture.
Understanding the Runtime Visibility Gap
Most cloud security frameworks emphasize pre‑deployment and configuration hardening. However, real threats often emerge while workloads are actively running. Runtime gaps arise because:
- Static scanners cannot detect malicious behavior inside containers.
- Cloud provider controls do not observe processes executed inside pods.
- Zero‑day exploits are often detectable only through behavioral anomalies.
- Logs alone cannot correlate kernel events with Kubernetes metadata.
Falco is specifically engineered to bridge this gap by analyzing real‑time system activity at the kernel level and mapping it to Kubernetes context.
Falco’s Intelligence Layer: How It Observes Behavior?
Falco operates by monitoring system events that include process execution, file interactions, privilege transitions, and network communications, directly from the node’s kernel event stream. It then correlates these observations with pod‑level metadata such as namespaces, deployment labels, service accounts, and container image sources.
Its rule engine doesn’t rely on known signatures. Instead, it interprets actions that diverge from the expected behavior of a workload. This makes Falco highly effective against unknown threats, insider misuse, and post‑exploit activity.
Key Value Areas of Falco in OKE Environments
Falco meaningfully strengthens OKE security through several high‑impact capabilities:
- Real‑time syscall‑level monitoring of containers and nodes.
- Automated detection of behavioral deviations.
- Deep contextual awareness of Kubernetes components.
- Early identification of security incidents.
- Clear and actionable alerts via routing frameworks.
By combining infrastructure signals with application behavior, Falco provides a holistic view of runtime activity that traditional controls cannot achieve.
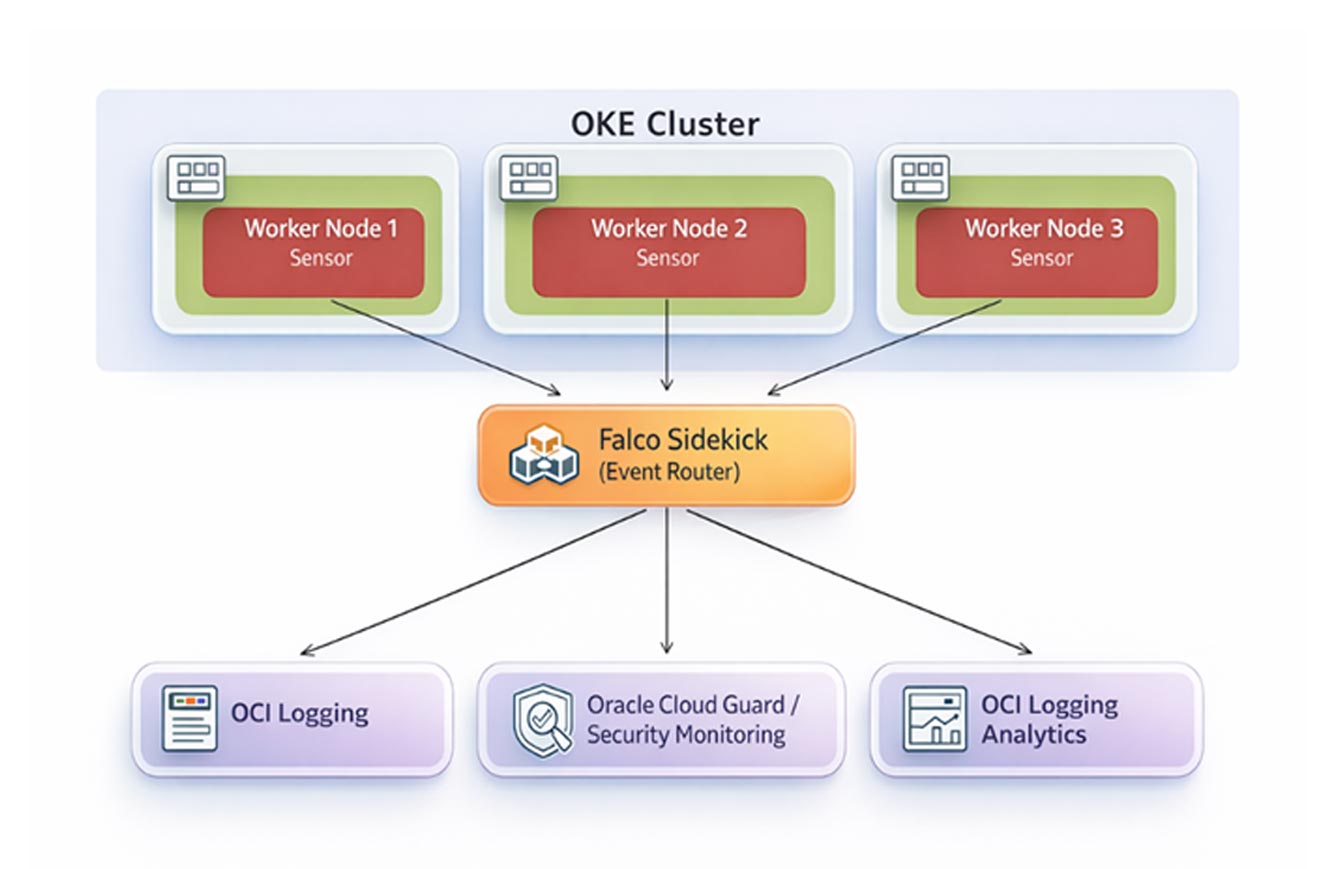
Architecture Overview
Falco integrates into an OKE cluster as a distributed layer of monitoring agents. Deployed as a DaemonSet, it ensures that every worker node is instrumented with a runtime sensor capable of interpreting kernel‑level events. Falco’s rule engine evaluates these events independently on each node.
For alert distribution and observability, Falco pairs with Falco Sidekick, a companion service that routes detection outputs to multiple backends, including logging systems, notification frameworks, SIEM pipelines, and dashboards.
Runtime Security Use Cases in OKE
Falco enhances operational security by providing visibility into several high‑risk scenarios:
- Unauthorized Container Shell Access: Detects attempts to open interactive shells inside containers, a strong indicator of compromise.
- Suspicious File System Modifications: Identifies abnormal writes or access to protected directories, system files, or sensitive application paths.
- Unexpected Process Execution: Highlights rogue binaries, downloaded payloads, or execution patterns associated with malware or crypto‑mining.
- Internal and External Networking Anomalies: Flags unusual outbound connections, unauthorized internal communication, and potential lateral movement.
- Privilege Escalation Behaviors: Detects sudden increases in process privileges, modifications to user/group IDs, or elevation attempts.
Kubernetes Activity Monitoring: Tracks pod lifecycle operations, suspicious API calls, and service account misuse to expose abuse or misconfigurations.
Operational Integration and Alert Routing
Falco’s alerting layer becomes significantly more powerful when paired with Falco Sidekick. Sidekick distributes Falco detections to a variety of destinations simultaneously, including:
- Logging and monitoring systems
- Slack, Teams, or email notifications
- SIEM and SOC pipelines
- Dashboards for visual analysis
This modular routing model ensures that runtime detections are easily consumable by operations, security, and incident response teams.
Strategic Impact for the Organization
The adoption of Falco underscores a proactive approach to Kubernetes security. Its strategic benefits include:
- Better defense against unknown threats and post‑exploit activity.
- Strong alignment with Zero‑Trust and DevSecOps practices.
- Enhanced compliance evidence for frameworks such as SOC2, PCI, HIPAA, and ISO 27001.
- Minimal operational overhead due to lightweight node‑level deployment.
- Deepened observability by merging behavior analytics with existing OCI monitoring layers.
Conclusion
Falco provides a powerful, behavior‑driven perspective into what workloads are actually doing inside an OKE cluster. By delivering real‑time insights, detecting deviations instantly, and integrating seamlessly with alerting ecosystems, it fills a critical blind spot left by traditional controls. Adopting Falco represents a significant uplift in runtime security maturity, strengthening resilience and trust across our cloud‑native environments.